Ever spun up a <a href="/tag/curl/">curl</a> command to debug a gnarly backend bug, only to be greeted by CloudFront’s infuriatingly vague 400 ERROR: The request could not be satisfied? You check your backend logs, nothing. CloudFront logs? Zilch. The request ID itself seems to evaporate into the ether. This isn’t magic; it’s a subtle miscommunication, and the culprit is often hiding in plain sight within your own curl command.
This isn’t just an edge case for junior devs trying to reproduce a bug. We’re talking about senior engineers, armed with their meticulously crafted curl incantations, staring at a wall of 400 Bad request with no clear path forward. The backend is fine. The CloudFront distribution should be fine. Yet, the request dies a silent, unlogged death somewhere in the AWS edge network.
Why the Black Hole?
The core of the issue lies in how CloudFront and its associated services, like AWS WAF (Web Application Firewall), process incoming HTTP requests. These systems are designed with security and efficiency in mind, and they have strict rules about how requests are formed. When a curl command, or any client-generated request, violates these unspoken rules, the request can be summarily rejected before it even hits your origin servers or generates meaningful logs.
The Request ID provided in the CloudFront error page is often a red herring in these scenarios. It’s generated at the edge, but if the request is malformed enough to be dropped before it’s fully processed by WAF or CloudFront’s logging mechanisms, that ID might not appear in any subsequent logs. So, the absence of backend or CloudFront logs for a given Request ID doesn’t mean your origin is healthy; it means the request never truly arrived for comprehensive processing.
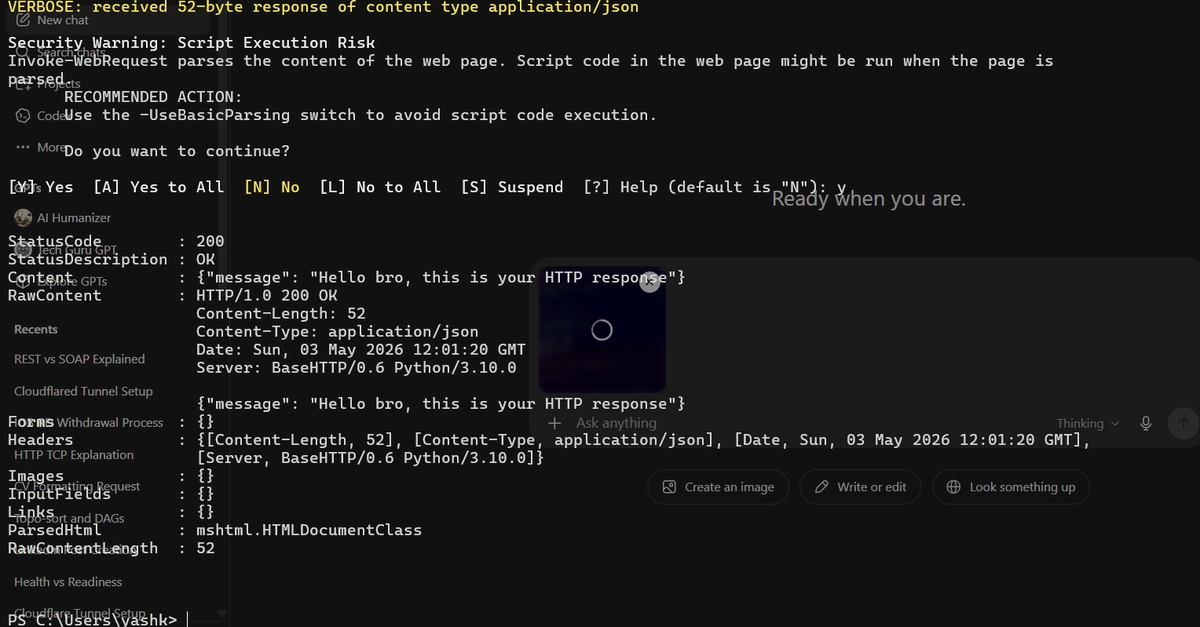
Second, the request got blocked from WAF, as in the strange response said Last resource, taking a look to curl itself, there is a header that silently drop the request at edge location and no proper error return, there is ‘content-length’
This quote nails it. The response mentions WAF, implying it might be the blocker, but the real investigation leads back to the client’s request itself.
The Silent Killer: Content-Length
Here’s the kicker: the header that often triggers this silent rejection is Content-Length. On the surface, Content-Length is a fundamental HTTP header. It tells the server exactly how many bytes to expect in the request body. It’s crucial for parsing requests correctly and preventing issues like HTTP Request Smuggling, where an attacker might craft a request that a front-end server parses differently than a back-end server, leading to security vulnerabilities.
CloudFront, WAF, and many other sophisticated load balancers and API gateways are acutely aware of this. They scrutinize Content-Length meticulously. If this header doesn’t accurately reflect the actual size of the request payload—perhaps due to malformed encoding, chunked transfer encoding mishandling, or simply an incorrect manual calculation in a curl command—the system can flag it as suspicious or malformed and drop it immediately. The problem is, this rejection can happen so early in the request lifecycle that it bypasses standard logging, leaving you scratching your head.
Cleaning Your curl Commands
So, what’s the fix? The next time you’re faced with this cryptic 400 error and your logs are empty, start by scrutinizing your curl command. Specifically, look for and consider removing potentially problematic headers that might be miscalculated or unnecessary for your specific debugging scenario. Content-Length is a prime suspect.
If you’re manually constructing a curl request and aren’t dealing with a very specific payload size requirement, it’s often safer to let the client handle chunked encoding or omit Content-Length altogether. The server will typically figure out the body size on its own. This small tweak can prevent your debug request from being silently discarded by upstream security measures.
This highlights a broader, often unstated, tension in modern cloud infrastructure: the increasing strictness of edge services versus the flexibility developers need for debugging. While security measures like WAF are essential, their bluntness can sometimes create opaque failure modes for legitimate traffic, especially when using tools like curl that offer granular control but also the potential for error.
This isn’t about the end of curl or even CloudFront. It’s about understanding the evolving landscape of request processing and security at the network edge. The 400 ERROR: The request could not be satisfied might be vague, but the underlying cause—a mismatch in expected request framing—is a deep architectural concern.
Why Does This Matter for Developers?
This issue forces a re-evaluation of how we treat debugging tools like curl. It’s not just a simple conduit for sending requests; it’s a client that interacts with a complex network of security and traffic management systems. Understanding how these systems interpret headers like Content-Length becomes as important as understanding your backend code. Developers need to be more mindful of the headers they send, especially when troubleshooting.
**
🧬 Related Insights
- Read more: Magic Link Auth: Are Passwords Officially Dead?
- Read more: Node.js Speed: 200ms API Calls Halved in Tests [DevTools Feed]
Frequently Asked Questions**
What does a 400 error from CloudFront mean? A 400 error from CloudFront typically means the request itself was malformed or invalid, preventing CloudFront from processing it. This could be due to issues with headers, request syntax, or security policy violations.
How can I fix the ‘request could not be satisfied’ error?
Start by examining your curl command or client request for malformed headers, particularly Content-Length. Ensure it accurately reflects the payload size or consider removing it if unnecessary. Check AWS WAF rules if applicable.
Does CloudFront log dropped requests? CloudFront logs requests that are processed, but malformed requests dropped at the earliest edge layers, before extensive processing, might not generate detailed logs or a traceable request ID in the standard logs.