When did we collectively decide that remembering a dozen unique, complex passwords was the pinnacle of digital security? It’s a question that lingers, especially as we see systems like passwordless magic links quietly gaining ground. This isn’t just another trend; it feels like a fundamental architectural shift in how we grant access to our digital lives. And the underlying mechanics are surprisingly straightforward, yet profoundly impactful.
Magic link authentication, in its essence, is about replacing the cognitive burden of passwords with a time-bound, single-use URL sent directly to a user’s inbox. The server generates a unique token, embeds it in a link, fires it off, and upon a user’s click, validates that token to grant access. Simple. Elegant. And, dare I say, rather intelligent.
A magic link is a unique URL sent to a user’s email. When the user clicks the link: The server verifies the token. The user becomes authenticated. No password is required.
At DevTools Feed, we’ve always had a soft spot for solutions that cut through complexity. The <a href="/tag/auth-verify/">auth-verify</a> library, as detailed in its documentation, offers a surprisingly lean path to implementing this. It abstracts away much of the cryptographic heavy lifting and token management, allowing developers to focus on the user experience and the business logic. Installing it is a quick npm install auth-verify, a familiar starting point for any Node.js developer.
The setup involves instantiating the AuthVerify class, providing a secret key, an expiry duration for the magic links, your application’s URL, and a token store. The choice of memory for development is fine, but production environments, as the docs rightly point out, should lean towards more persistent solutions like Redis. This hints at the scalability considerations developers must keep in mind—even with passwordless systems.
Configuring email transport is where the rubber truly meets the road. Whether you’re a Gmail power user needing an app-specific password, or leveraging strong services like Mailgun, SendGrid, or Resend, the library offers flexible integration points. Each requires specific credentials, and for services like Mailgun, domain verification is often a prerequisite. This stage, while seemingly mundane, is critical for ensuring that the magic actually reaches the user’s inbox.
Why Magic Links Are Gaining Traction
It’s easy to dismiss magic links as a novelty, but their appeal runs deeper than mere convenience. For businesses, especially SaaS providers, they significantly reduce the friction in user onboarding and login flows. Think about the sheer volume of password reset requests that plague support desks; magic links can drastically diminish that overhead. From a security standpoint, they eliminate the risk of weak or reused passwords, a persistent vulnerability in traditional authentication models. An attacker can’t brute-force a password they don’t need to know. The ephemeral nature of the link, coupled with its unique token, creates a strong, albeit different, security posture.
Furthermore, the modern user’s expectation is for experiences that are as frictionless as possible. We’ve grown accustomed to one-click checkouts and instant access. Expecting users to juggle multiple passwords for different services feels increasingly anachronistic. Magic links fit this evolving user psychology perfectly. They’re intuitive, require minimal cognitive load, and when implemented correctly, feel incredibly responsive.
Building the System: The Code Behind the Magic
Let’s talk code. Sending a magic link is handled by auth.magic.send('[email protected]', { ... }). The {{link}} placeholder within the HTML email template is a clever touch, automatically injecting the generated, secure URL. This templating mechanism simplifies email creation, allowing developers to embed dynamic content without complex string manipulation.
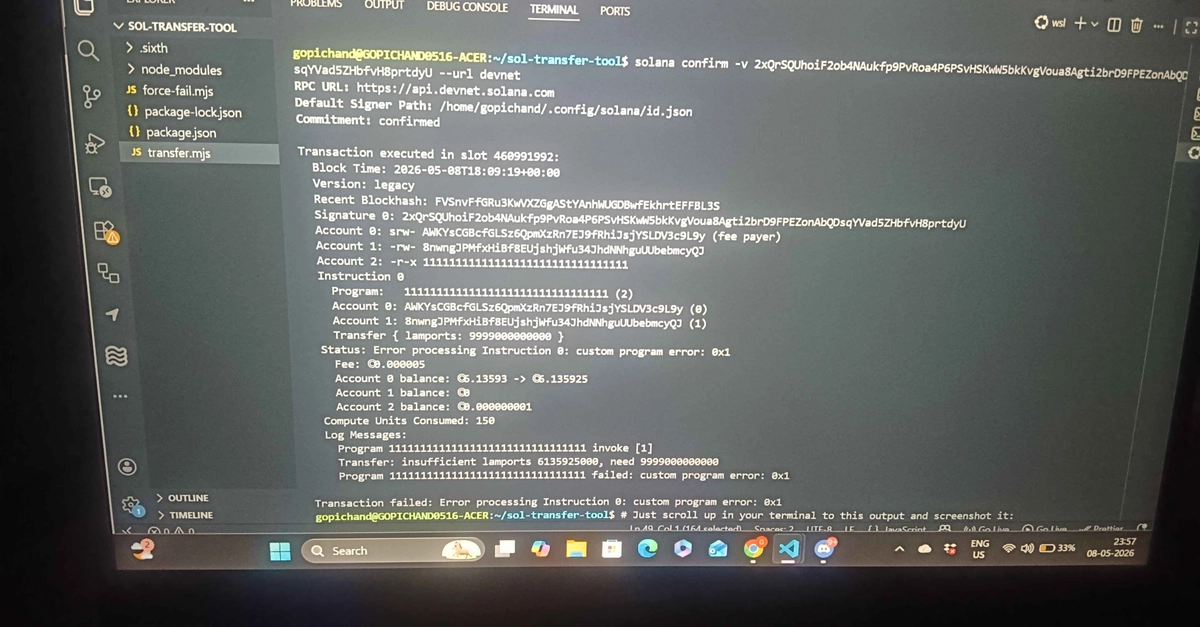
The real action, however, happens on the backend when a user clicks that link. A typical /auth/verify route on your Express server intercepts the request. It extracts the token from the query parameters and passes it to auth.magic.verify(token). If the token is valid and hasn’t expired, the library returns user data; otherwise, it throws an error, which your application can then gracefully handle, perhaps by presenting the user with an option to resend the link.
Here’s a snapshot of that verification logic, as provided:
app.get('/auth/verify', async (req, res) => {
const { token } = req.query;
try {
const user = await auth.magic.verify(token);
res.json({ success: true, user });
} catch (err) {
res.status(400).json({ success: false, message: err.message });
}
});
This concise snippet showcases the power of abstraction. The auth-verify library handles the complex validation of the token’s signature, its expiry, and its presence in the store. The developer’s job is to manage the response—whether it’s redirecting the user to their dashboard or presenting an error message.
The library isn’t just for verification, either. It can orchestrate the entire flow. A common pattern involves a POST request to /auth/send which takes an email address, triggers the auth.magic.send method, and responds with a confirmation message. The full example, demonstrating both sending and verifying within a single Express app, underscores the simplicity of integrating this authentication method.
const express = require('express');
const bodyParser = require('body-parser');
const AuthVerify = require('auth-verify');
const app = express();
app.use(bodyParser.json());
const auth = new AuthVerify({
mlSecret: 'supersecretkey',
appUrl: 'http://localhost:3000',
storeTokens: 'memory'
});
auth.magic.sender({
service: 'gmail',
sender: '[email protected]',
pass: 'your_app_password'
});
// Send link
app.post('/auth/send', async (req, res) => {
const { email } = req.body;
await auth.magic.send(email);
res.json({ message: 'Magic link sent!' });
});
// Verify link
app.get('/auth/verify', async (req, res) => {
try {
const user = await auth.magic.verify(req.query.token);
res.json({ message: 'Login successful!', user });
} catch (err) {
res.status(400).json({ message: err.message });
}
});
app.listen(3000, () => console.log('🚀 Server running on port 3000'));
This code is lean, functional, and demonstrates a complete, albeit basic, magic link authentication system. It’s the kind of pragmatic solution that makes you question why we ever settled for the password-laden status quo.
The Unique Insight: While magic links offer a more secure and user-friendly alternative to passwords, their widespread adoption hinges on strong token management and effective email delivery infrastructure. The auth-verify library simplifies the former, but developers still need to ensure their chosen email service is reliable and configured correctly. A failure in email delivery renders the entire system useless, a critical dependency that isn’t always obvious until it breaks.
🧬 Related Insights
- Read more: Teapot Enterprise Platform: Devs Roast Over-Engineered SaaS with a Useless Teapot API
- Read more: Dead Code Erased $440 Million from Knight Capital in Just 45 Minutes
Frequently Asked Questions
Will magic links replace passwords entirely?
It’s unlikely they’ll replace passwords entirely in the immediate future, especially for highly sensitive applications or legacy systems. However, for many consumer-facing apps and internal tools, they’re rapidly becoming the preferred method due to their ease of use and enhanced security. Expect hybrid approaches to persist for some time.
How secure are magic links compared to traditional passwords?
Generally, magic links are considered more secure. They eliminate the risks associated with weak, reused, or compromised passwords. The security relies on the cryptographic strength of the token and the secure transmission of the email. However, the security of the user’s email account itself becomes paramount.
What are the limitations of magic link authentication?
The primary limitation is the reliance on email as the delivery mechanism. If a user’s email account is compromised, or if there are delivery issues, access can be disrupted. Additionally, for users who don’t frequently check their email, the login process might feel less instant compared to remembering a password.