Databases & Backend
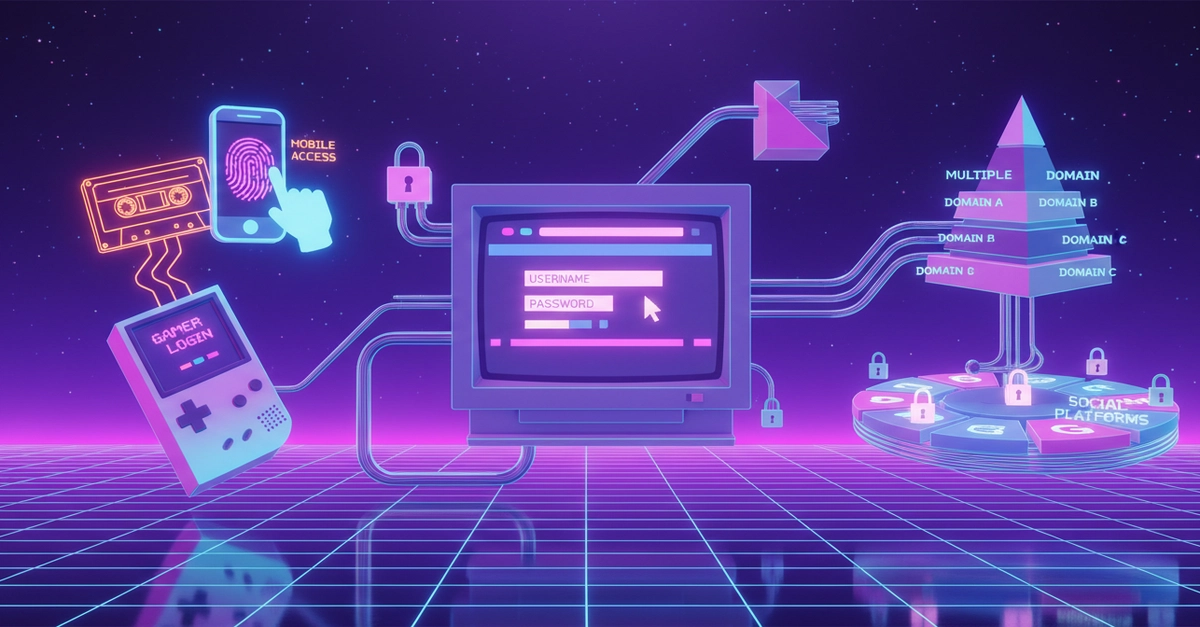
Auth Strategies: Your App's Invisible Security Superpower
Auth wars rage on, but here's the map to peace: eight strategies, each a hero in its arena. No more guesswork — just tools that fit your fight.