For developers, the advent of AI agents has been a double-edged sword. They offer immense promise for productivity, churning out code, debugging, and even architecting solutions. Yet, beneath the surface of these sophisticated tools lies a bewildering torrent of data — prompts, code snippets, diagnostic logs, sensitive API keys, and raw telemetry — all flowing across the network, largely unseen and unmanaged.
This is precisely the void that Agent Shield, a new open-source project, aims to fill. It doesn’t just put a window into this data flow; it puts a control panel there.
Why Does This Matter for Developers?
Think about it. You’re using an AI agent to refactor a critical piece of your application’s codebase. It’s sending parts of that code, along with your internal server details, and potentially even secrets to an external LLM. Without a mechanism to inspect or control this egress, you’re operating on faith. Faith that the AI vendor’s security is impeccable. Faith that no accidental exposure will occur. Faith that your proprietary algorithms won’t end up in a future training dataset.
Agent Shield tackles this head-on by acting as a traffic control layer. It sits squarely between your AI agent and the network, offering developers the ability to:
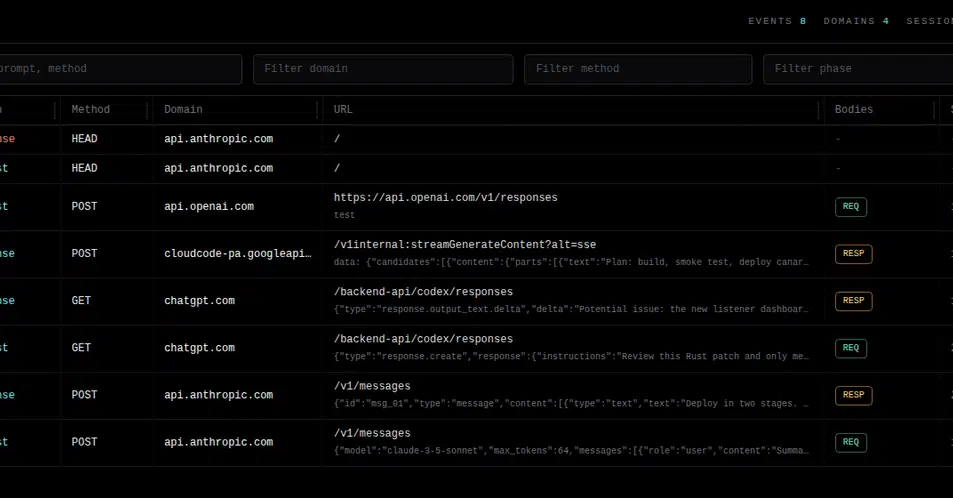
- See Everything: Inspect HTTP, WebSocket, and Server-Sent Events (SSE) traffic in real-time. No more guessing what the agent is actually communicating.
- Audit with Precision: Record every outgoing request. Details like destination, source tool, timestamp, and any applied decision are logged, providing a strong audit trail.
- Guard Sensitive Data: Implement Data Loss Prevention (DLP) measures. Block secrets, private code, customer data, or internal logs before they ever leave your machine. This can be done via custom rules, local classifiers, or even a local LLM for sophisticated analysis.
- Modify Traffic: Redact sensitive information, replace payloads, block malicious requests, or reroute traffic as needed. It’s active intervention, not just passive observation.
- Optimize Model Usage: Route simpler tasks to local models (via Ollama or llama.cpp) while sending complex queries to external APIs. This isn’t just about cost; it’s about efficiency and keeping sensitive workloads in-house.
- Control Spending: Attach counters, budgets, latency rules, and project-specific policies directly to the AI client’s network activity, independent of the vendor’s pricing model.
- Orchestrate Agents: Coordinate multiple CLI agents through a single traffic layer, eliminating the need for custom per-client integrations.
- Monitor Worker Status: Gain insight into which agent is busy, free, what task it’s performing, and if it’s encountering any blockages.
- Set Up Alerts: Plug in listeners for Telegram, dashboards, or analytics to proactively notify you of critical events.
- Maintain Client Independence: Keep control of your AI interactions outside the vendor’s UI, pricing changes, and telemetry settings. This is a crucial point for long-term strategy.
The Hidden Cost of the Black Box
Historically, the network traffic of developer tools has been treated as an afterthought, often buried within command-line interfaces (CLIs). While terminal control is useful for immediate debugging, it doesn’t answer the fundamental question: What exactly is being transmitted? Agent Shield’s core value proposition is to transform this black box into a transparent, controllable pipeline.
The idea is simple: AI agents send a lot of stuff over the network: prompts, code snippets, logs, tool output, telemetry, sometimes secrets. Most of that is hidden inside the CLI.
This isn’t just about security theater; it’s about operational integrity and strategic autonomy. As AI agents become more deeply integrated into development workflows, the potential for unintended data leakage or compliance violations grows exponentially. For organizations handling sensitive intellectual property or customer data, this represents a tangible risk. For individual developers, it’s about maintaining control over their tools and the data they process.
Agent Shield introduces two key extension points: Listeners, which passively collect event data for logging and monitoring, and Decision Handlers, which actively intercept and can modify or block traffic before it proceeds. This architecture allows for flexibility, enabling everything from basic logging to sophisticated DLP enforcement.
What’s particularly compelling here is the independence it offers. The proliferation of AI coding assistants, each with its own proprietary API, pricing, and telemetry, creates a vendor lock-in scenario that developers often find themselves trapped in. Agent Shield attempts to abstract this away, putting the control back into the hands of the user, not the service provider.
This project echoes early efforts in network security and observability where visibility was paramount. Consider the rise of network proxies and sniffers in the early days of the internet, or more recently, service meshes in the microservices era. Each represented a move to understand and control complex, distributed systems. Agent Shield is doing for AI agent communication what those tools did for their respective domains.
There’s a clear market dynamic at play: as AI tools become more powerful and ubiquitous, the need for governance and transparency will only intensify. Agent Shield’s open-source nature democratizes this capability, preventing it from becoming a premium feature only accessible through expensive enterprise solutions.
What’s Next for Agent Shield?
The project is still in its nascent stages, but the foundational pieces are in place: an MITM proxy, strong handling of common web protocols, normalized event streams, REST listeners, and a dashboard for captured traffic. The ambition is clear: to provide a comprehensive, client-independent layer of control over AI agent network interactions.
For organizations and individual developers alike, Agent Shield offers a much-needed layer of sanity in the rapidly expanding, often opaque, world of AI-powered coding assistants. It’s a step towards making these powerful tools not just productive, but also safe and manageable.