Auth Strategies: Your App's Invisible Security Superpower
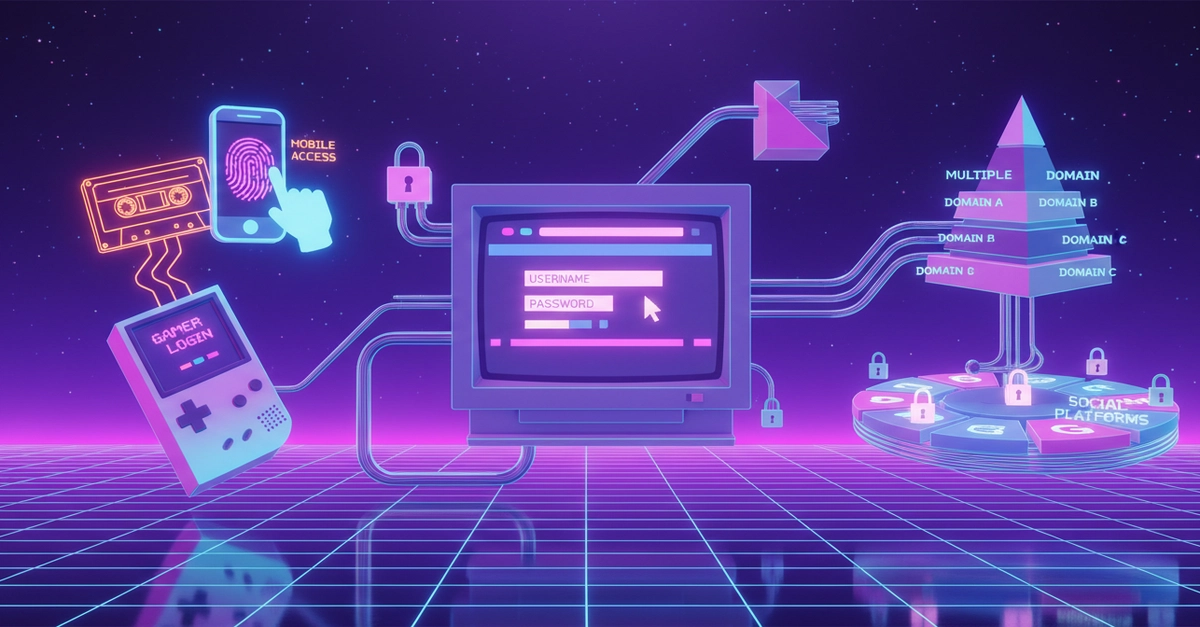
Auth wars rage on, but here's the map to peace: eight strategies, each a hero in its arena. No more guesswork — just tools that fit your fight.
⚡ Key Takeaways
- No universal auth winner — match strategy to scenario for security and scale.
- Sessions excel in revocation and server control; JWTs in stateless speed.
- Hybrid patterns like JWT access + refresh cookies rule modern SPAs.
Worth sharing?
Get the best Developer Tools stories of the week in your inbox — no noise, no spam.
Originally reported by dev.to